Pixel-level receipt checks for finance teams without the friction
Oct 1, 2025
- Team VAARHAFT
(AI generated)
What if the next suspicious receipt in your queue was edited with a tap, not a scalpel? Reports of manipulated claim photos are rising, with investigators in 2024 flagging simple app edits that add fake damage to vehicles and inflate payouts (The Guardian). At the same time, new provenance standards for digital media are gaining traction but are far from universal adoption. Finance leaders face a practical question that blends risk, UX and compliance: how can finance teams intelligently check receipts at pixel level for duplicates, stock images and edits without burdening honest users?
This article lays out a pragmatic approach for insurers, banks and enterprise finance teams. We show which low-friction checks deliver fast signal, when to escalate to pixel-level forensics and how to add a secure re-capture step that respects customers while shutting down fraud. Along the way we reference benchmarks such as the NIST Open Media Forensics Challenge and content provenance efforts like C2PA.
Why pixel-level checks matter for finance teams
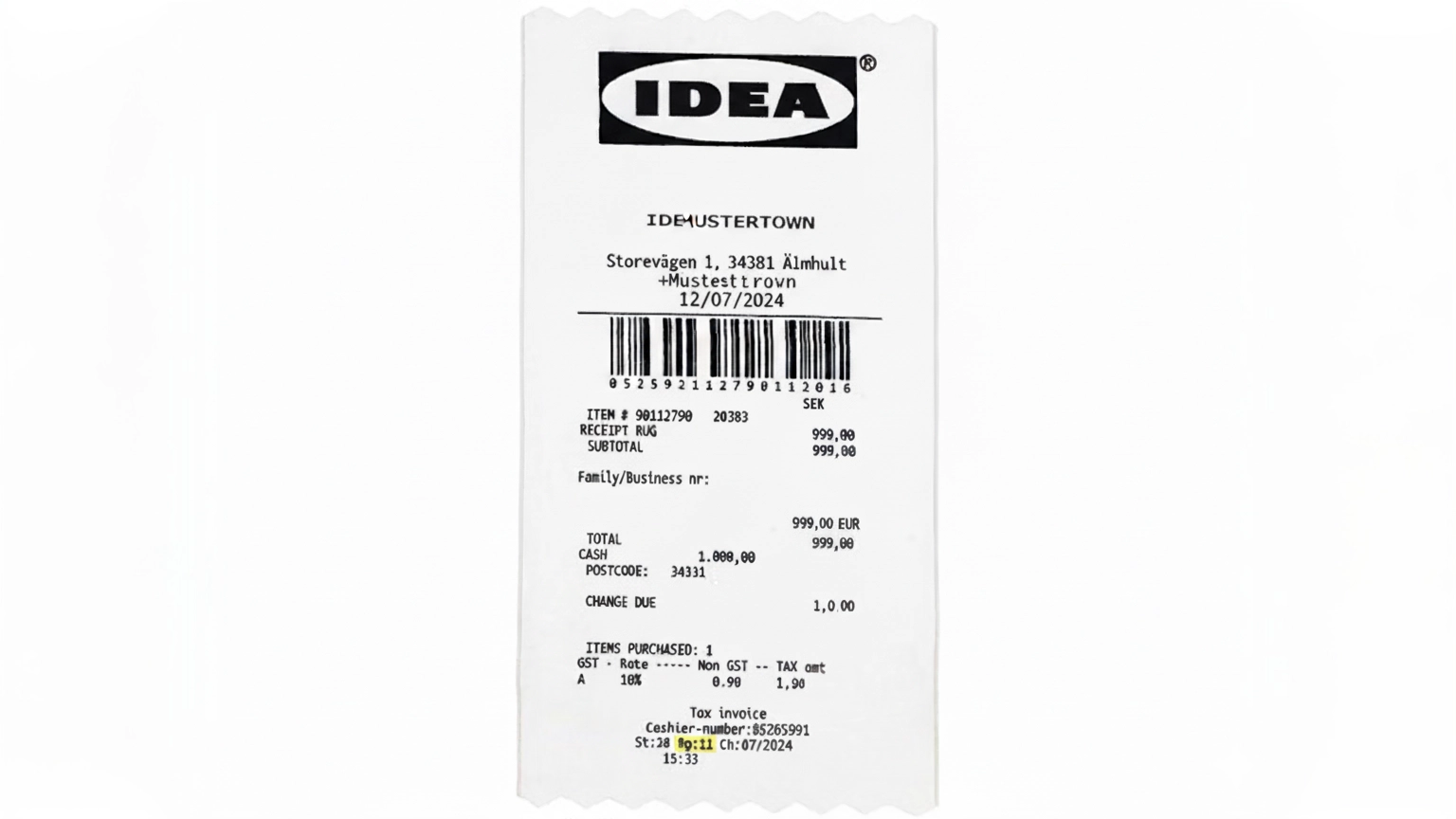
Fraudsters exploit AI and consumer-grade editors to submit synthetic or manipulated evidence. In finance workflows this surfaces as duplicate receipts reused across claims, stock photos masquerading as proof of purchase and shallow edits that change totals, dates or visible damage. Research surveys detail how manipulation ranges from simple copy-paste to sophisticated deepfake-style generation, with detectors needing both localization and robust classification to keep up (MDPI, Deepfakes Survey).
The business stakes are clear. If detection is too lax, payouts and chargebacks increase. If detection is too aggressive, false positives pile up and customers abandon claims or onboarding. Pixel-level verification for receipts should therefore be risk-based, explainable and as invisible as possible to honest submitters.
A few distinctions help decision makers frame the strategy. Deepfakes refer to content generated or heavily altered by AI systems, while conventional manipulation covers edits with photo tools or mobile apps. Authenticity asks whether the file shows signs of tampering. Originality asks whether the content is genuinely captured for this case or copied from elsewhere, for example a stock image. Both require different signals in the pipeline.
When to escalate to pixel localization
For receipts or claim photos that trigger medium or high risk, escalate to pixel-level localization. Sensor pattern noise analysis can corroborate whether a camera captured the image and help localize splicing. Academic work on photo-response non-uniformity demonstrates how camera fingerprints aid tamper detection, while also noting anti-forensic caveats.
Modern tools can produce heatmaps that highlight edited regions on a document or photo. This makes review faster and more explainable for finance teams and auditors. It also helps resolve disputes with a clear, visual rationale that aligns with audit requirements.
Privacy and UX guardrails
To avoid burdening honest users, design pixel-level verification as an invisible background step. Run automated checks ephemerally, delete media immediately after analysis, and store only anonymized fingerprints and human-readable reports. Favor probability-based scores and risk-based step-ups over blunt denials.
Implementation blueprint for claims and finance operations
A three-stage workflow
A layered pipeline balances speed, accuracy and customer experience for image forensics in finance teams. It aligns with a simple principle: low-friction checks first, targeted pixel-level evidence second and human intervention only when needed.
- Automated triage. On upload, extract metadata and provenance, run reverse and semantic image search and skim for obvious artifacts. Most duplicate or stock image fraud is caught here. For a deeper dive into provenance strengths and gaps, see our overview of the standard and its limitations.
- Pixel-level forensic localization. For medium or high-risk items, run localization and source validation. Heatmaps that mark edited pixels on receipts or claim photos accelerate review and support consistent decisions.
- Human review and secure re-capture. If evidence remains inconclusive, route to a human reviewer and invite the submitter to capture fresh, time-verified photos through a secure web camera flow. This keeps honest users moving while blocking screen or print re-photography attempts.
Technical and process safeguards to reduce false positives
- Keep first-pass checks sub-second and fully automated. Escalate only when the risk score crosses a threshold tied to transaction value or policy.
- Treat verified provenance as a strong trust signal. Signed Content Credentials can materially reduce manual handling when present.
- Offer an effortless, no-app re-capture path for escalations and expired evidence. Make it available by SMS to minimize drop-off.
- Minimize data retention. Log audit conclusions and anonymized image fingerprints rather than storing media, and delete originals right after analysis.
- Document your decision logic with explainable artifacts. Pixel heatmaps and signed reports help risk, compliance and external audits.
Risks, adversarial trends and regulatory context
Adversarial tactics to watch
Attackers adapt quickly. Studies show that adversarial perturbations and re-encoding strategies can degrade some deepfake detectors, which underscores the need for layered defenses and provenance signals rather than a single classifier (arXiv 2023). Triage methods should be robust to re-saves and downscaling, and pipelines should log when inputs arrive from messaging apps or social platforms that strip metadata.
Regulatory and standards landscape
Finance teams must align image and document checks with privacy and AI governance. The EU AI Act introduces obligations for transparency and risk management for AI systems, while data protection rules require data minimization and clear purposes for processing.
For deeper context on the fraud landscape and underwriting exposure, see our analysis on how digital manipulation reshapes risk selection and claims handling here.
Conclusion: a pragmatic path that protects users, not burdens them
Pixel-level receipt checks do not need to punish honest customers. The path forward is layered and low friction. Begin with automated, privacy-preserving triage that extracts provenance, detects duplicates and flags obvious edits. Escalate only where risk warrants it, and explain decisions with pixel localization that reviewers can trust. Where evidence is inconclusive, invite a secure re-capture that confirms reality without forcing users through complex steps.
If you are evaluating solutions to implement this pipeline, consider pairing fast forensic analysis with a secure re-capture option. For example, Vaarhaft’s image analysis provides pixel-level heatmaps, duplicate and stock detection, C2PA extraction and reverse image search in seconds, available via web or API (Fraud Scanner). When evidence needs fresh capture, a browser-based camera flow can verify that images come from real three-dimensional scenes and block screen or print re-photography attempts without an app or login (SafeCam).
.png)